how to properly target machines with the dfs management pack
Image by GravitysAppleNZ via Flickr
if you’re planning to install the microsoft windows dfs 2003 management pack (yes, the converted one), you should be certain to target properly. if you don’t, you’ll end up with some trash data coming from other dfs sources (e.g. domain controllers) that you may not want in your dfs views.
i spent a disproportionate amount of time on this to figure out all the ins and outs of targeting inside of this mp. i would love to say it was for my edification, but in actuality, it was because the agents apparently didn’t work right until they were restarted. :|
anyway, so the bottom line is, it was much easier than what i describe in this post on system center central. it may still be confusing to others however so i’m posting it here.
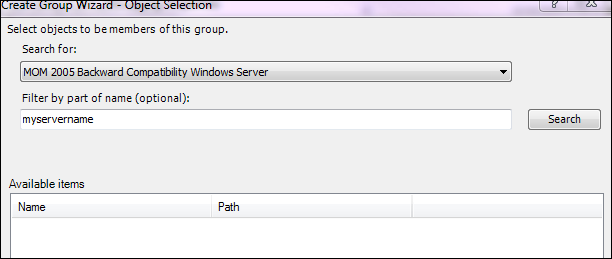
the first thing you’ll want to do is create a new group. there isn’t much to do here except target your members properly. i used something like this to target a few of my dfs servers. specifically, i’m using the mom 2005 backward compatibility windows server target since this is the target that one of the discovery rules uses later.
once that’s setup, open the object discoveries section. to make it simpler, change your scope to microsoft windows 2003 servers with distributed file system service installation.
you should find this discovery -
Microsoft.Windows.Server.DFS.Microsoft_Windows_2003_Servers_With_Distributed_File_System_Service_Installation.Discovery
- targeting the mom 2005 backward compatibility windows computer object.

this is the rule that you want to override.
- right-click the rule
- go to overrides > override the object discovery > for all objects of class: mom 2005 backward compatibility windows computer
- once open, choose override on the enabled parameter and change the override value to “false”.
- be sure to add this to your own, custom management pack.

now we’ve effectively blocked the discovery from executing against the class above (which subsequently includes damn near everything). before you go anywhere, let’s create another override.
- overrides > override the object discovery > for a group…
- choose the group that you created prior. the override value probably shows up as “true” already so this may appear counterintuitive.
- select the override anyway.
- again, add this to your own custom mp.

if done right, you should only see the dfs servers you targeted in the custom group you created. here’s how mine looks:

hope this helps!

Comments
Post a Comment