Search This Blog
notes, ramblings, contemplations, transmutations, and otherwise ... on management and directory miscellanea.
Posts
Showing posts from February, 2010
gartner’s key predictions for 2010 and beyond
- Get link
- X
- Other Apps
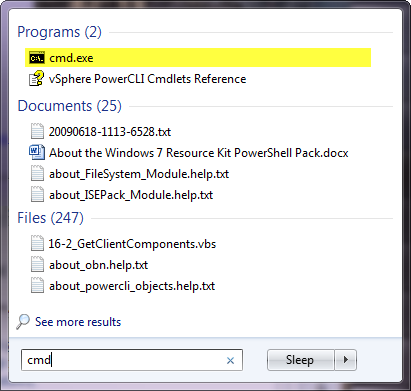
search programs and files no longer works in windows 7 (only shows headers)
- Get link
- X
- Other Apps