Deciphering userAccountControl
There’s been a lot of good information on userAccountControl (UAC) over the years. I was trying to explain a coworker about how it works which got me really thinking about it. I thought I’d try to share my findings with you in case you have a similar interest in learning it.
WHAT IS USER ACCOUNT CONTROL?
Let me first describe UAC. The simplest definition, in my opinion, would be to say that it’s a composite status of an object. (Let’s talk about user objects specifically.) A user object can be a variety of things -- disabled, enabled, locked, password expired, etc -- which when the integer value that’s stored in UAC is broken down, represents them. That’s why the account options are multi-select, I guess. :-)
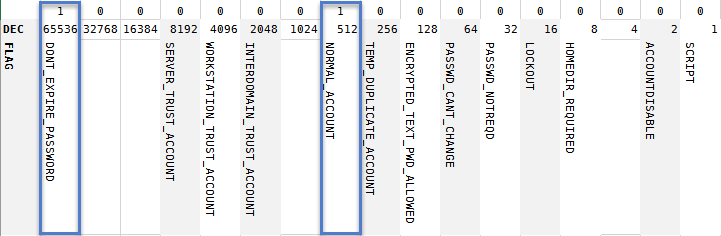
Note that UAC is a 32-bit value. Anyway, this is the LDAP attribute where Active Directory stores the various states of your user account. How many different states can a user account be in, you might be wondering? It’s documented in quite a few places, actually (and now here.)
(Sorry about the screenshot. I had ALL THE INTENTION in the world to actually make it copy/paste, but translations going into Live Writer wasn’t being my friend. I linked it to the article with the values though. :) One last note, if you look at the flag name, it’s pretty clear that not all of those states actually apply to user objects.)
INTRODUCING… OUR EXAMPLE
Let’s make this practical and figure out what we’re looking at. Suppose you were goofing around running queries looking at UAC and found an account of interest. The account has a value of 66048. If I run a bitwise AND against it based on the values in the above table, it breaks down into 65536 and 512.
Go on, check my math. 65536 + 512 = 66048.
I transposed the table above to make it easier to look at. Basically, 66048 translates to a normal account with a password that never expires. That makes sense so far right?
THE BINARY VIEW
When you convert 66048, you get the binary equivalent of 10000001000000000. If you look at the table above, there are definitely values that are missing -- like 1024. If we add those values back in and overlay our binary version of the UAC value, the 1s lay right over the state. Cool, huh?
BITWISE OPERATORS
I mentioned using bitwise AND earlier to figure out what UAC 66048 was composed of. I’ll get into that in my next post since you are probably still waking up from reading this one.




Comments
Post a Comment